
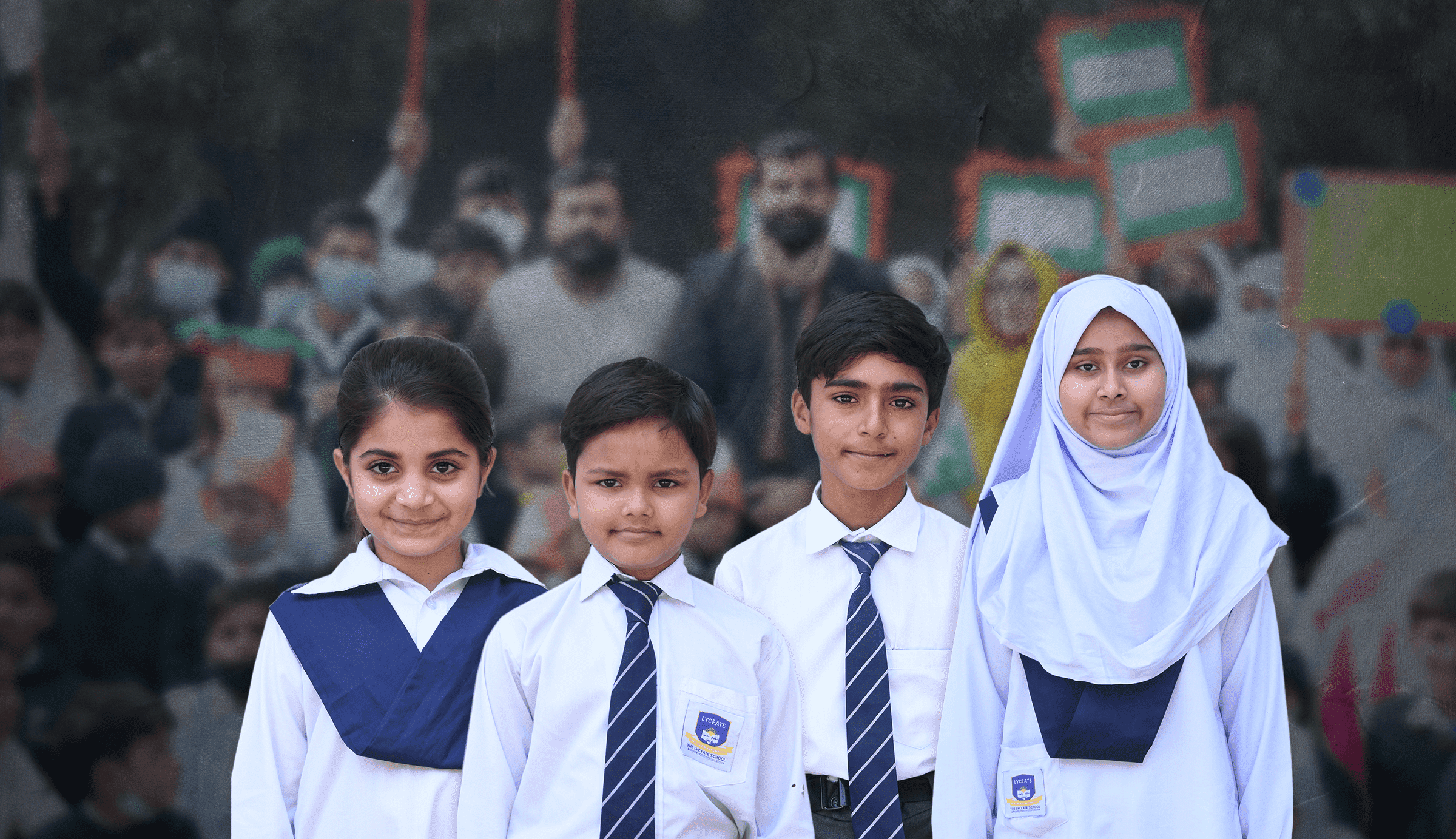

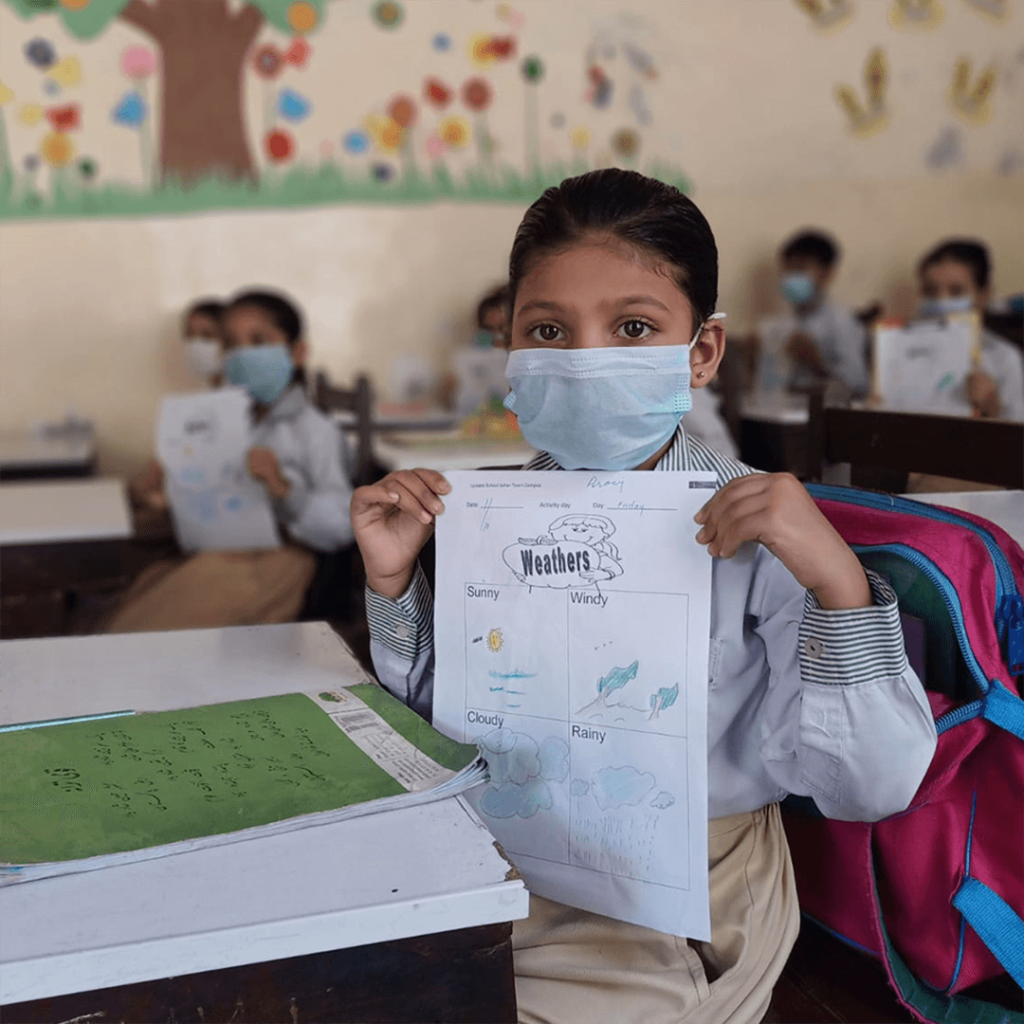
PCA prioritizes education through two elementary schools, aiming to educate underprivileged students and orphans. University students receive support via SJ & LA scholarships, overcoming financial barriers for higher education. Aligned with “Taleem, Tarbiat, Khidmat,” these efforts drive meaningful change by offering quality education and opportunities.

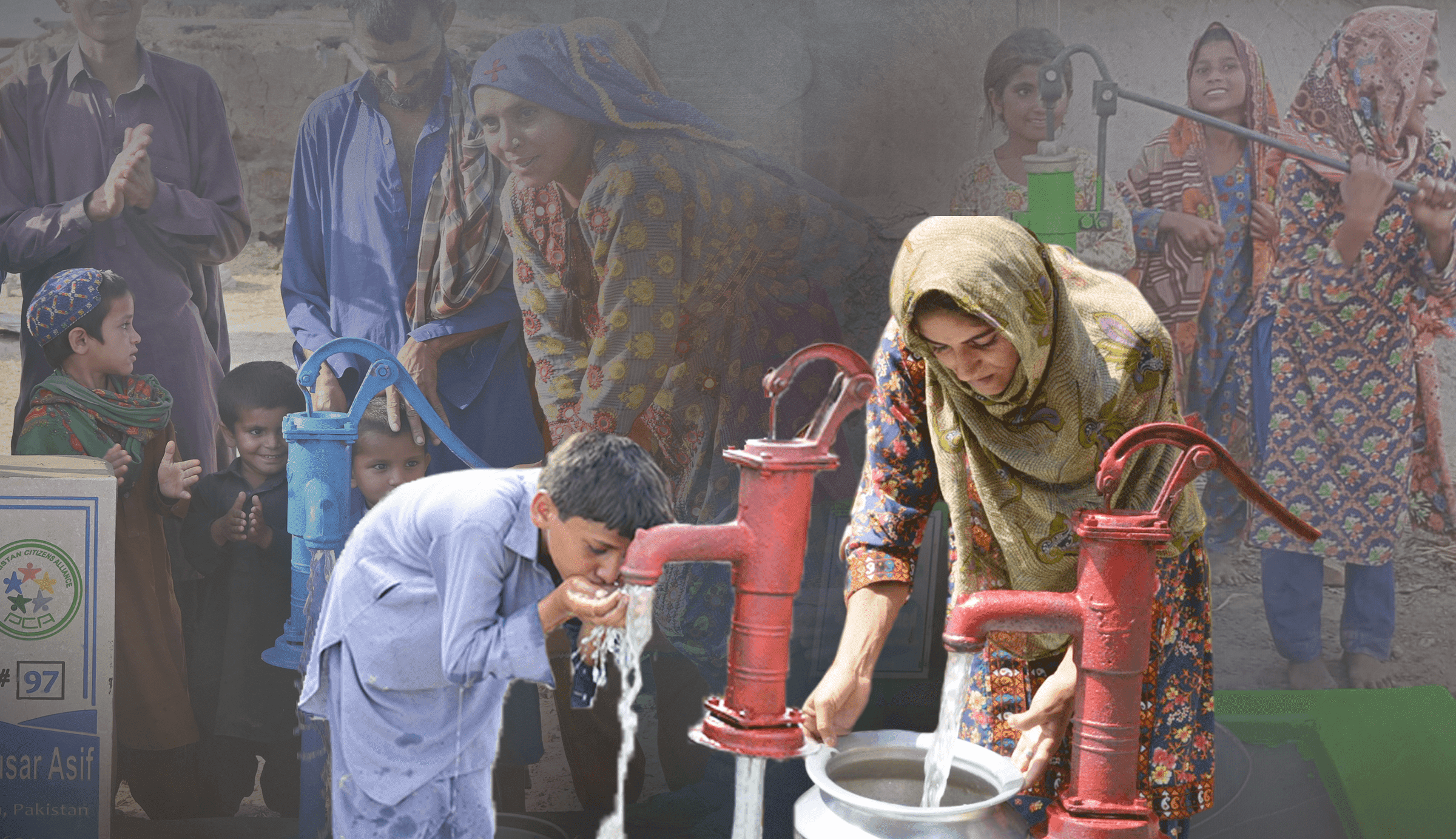
PCA has dedicated itself to uplifting underserved communities. Our diverse efforts cater to fundamental needs, affordable food, and healthcare. With projects like “Defeat the winter,” “Esaar e Ramazan,” and the “Qurbani Project,” “Eesaar Water Project”, Construction of Mosque we bring tangible change.

At Pakistan Citizen Alliance, we are committed to offering aid and relief during disasters and crises. Our strategic relief operations swiftly and effectively assist victims of various natural calamities. We have previously supported those impacted by events such as the Turkey earthquake, Israel-Gaza attacks, Pakistan floods, and more



Pakistan Citizens Alliance (PCA) (Registration Number RP/9154/L/S/14/, NTN 4600205) is a non-profit organization which was registered in 2014 under Pakistan’s Societies Registration Act , 1860/Companies Act. 2017. PCA is an approved NGO by Pakistan’s Federal Board of Revenue. For documentation review please click here